Fortinet Partners in Bangalore
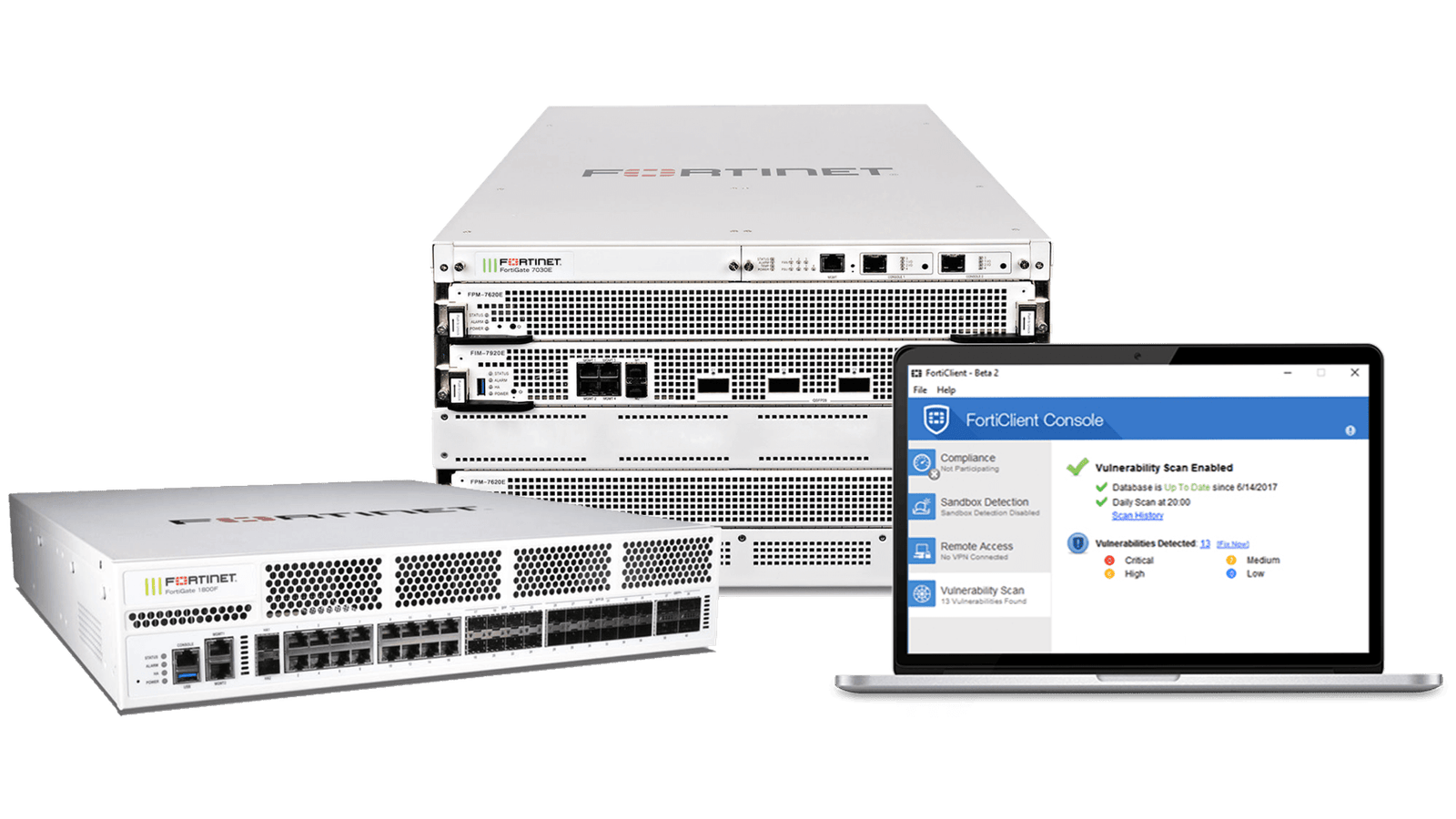
As Fortinet Partners, we provide complete Cybersecurity and Networking solutions
Why Vays Infotech?
With over 27 years of IT excellence, Vays Infotech stands out as one of the most reliable Fortinet partners in Bangalore. We are more than a service provider — we’re your dedicated cybersecurity ally, offering customized Fortinet solutions backed by certified engineers and 24/7 support.
Whether you’re looking to secure your enterprise with next-generation firewalls, adopt Zero Trust Access, or implement a robust Secure SD-WAN, Vays Infotech is your single point of contact for Fortinet cybersecurity solutions in Bangalore.
We specialize in:
- Advanced threat protection
- Secure network design
- Scalable architecture and cloud readiness
- Endpoint and operational technology (OT) security
Our deep expertise in Fortinet technologies ensures your business stays protected, agile, and compliant — no matter its size or sector.
Advantages of Fortinet solutions
Comprehensive, High-Performance Security
Fortinet delivers industry-leading protection through high-performance firewalls, threat detection systems, and secure access tools. At Vays Infotech, we bring these technologies to your doorstep — as your go-to Fortinet partners in Bangalore.
Advanced Threat Intelligence
Our solutions include deep packet inspection, IPS, anti-malware, and FortiGuard-powered real-time threat intelligence — stopping cyber threats before they impact your business.
Scalable and Future-Ready Architecture
Fortinet’s Security Fabric lets you scale securely across cloud, branch, and data center environments. Vays Infotech helps you deploy this architecture effectively to match your business growth.
Centralized Management & Visibility
We implement centralized tools like FortiManager and FortiAnalyzer for seamless policy management and complete visibility into your IT infrastructure.
Next-Generation Firewalls (NGFWs)
Fortinet NGFW Secures Every Layer of Your Network
These days, legacy firewalls are simply not enough for digital networks. Vays use of Fortinet’s Next-Generation Firewall solutions deliver deep traffic inspection, User identity awareness, and AI-driven threat intelligence, which protect against the latest cyber threats, whether they are in the cloud, remote, or a hybrid architecture.
From small offices to large public clouds or service providers, we have NGFWs that fit your environment, at the right price point, with the appropriate performance.
Entry-Level NGFWs
Entry-level Next-Generation Firewalls are ideal for small offices, retail environments, and remote branches. These models deliver essential security features like intrusion prevention, basic VPN, application control, and content filtering — all packaged in a compact, easy-to-manage form factor. Perfect for organizations with limited IT staff, they offer protection against common threats without unnecessary complexity.
Mid-Range NGFWs
Mid-range NGFWs are built for growing businesses, educational institutions, and regional offices that require stronger performance, security, and flexibility. These devices support full SSL/TLS inspection, integrate with real-time threat intelligence, and offer sandboxing for advanced malware detection. With built-in SD-WAN, centralized policy enforcement, and role-based access controls, they help maintain consistent security across expanding networks.
Enterprise NGFWs
Enterprise-grade NGFWs are designed for large-scale deployments such as data centers, government agencies, and service providers. They offer ultra-high throughput, advanced persistent threat (APT) protection, micro-segmentation for multi-tenant architectures, and deep integration with SIEM and identity management systems. These powerful firewalls are built for Zero Trust and hybrid cloud environments, providing scalable, automated, and highly intelligent network security.
Enterprise Models
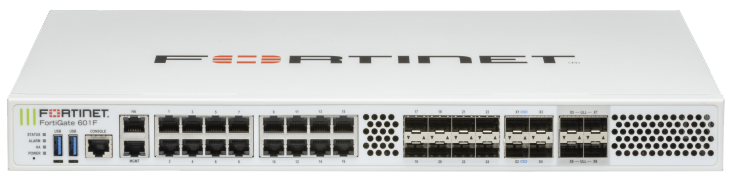
FortiGate 600 F
Threat Protection – 9 Gbps
USB Port – 1
Console Port – 1
GE RJ45 Ports – 16 (Including Internal, WAN, DMZ)
10GE SFP+ Slots – 8
GE SFP Slots – 8
100GE QSFP28 Slots – 0
Description
32x total ports including 16x GE RJ45, 8x 10GE SFP+ slots, & 8x GE SFP slots.
Designed for high-throughput threat protection, SD-WAN, and secure data center edge deployments.
Equipped with advanced hardware acceleration to support SSL inspection and encrypted traffic processing.
FG XX HA SKUs must be bought in pairs and entitle HA pair to leverage single service contracts (limited to Enterprise, UTP, and ATP bundles only).

FortiGate 3200 F
Threat Protection – 37 Gbps
USB Port – 1
Console Port – 1
GE RJ45 Management Port – 2
10GE SFP+ Slots – 32
100GE QSFP28 Slots – 4
40GE QSFP+ Slots – 4
Description
42x high-speed ports including 32x 10GE SFP+ slots, 4x 100GE QSFP28, 4x 40GE QSFP+, and 2x GE RJ45 management ports.
Built for hyperscale data centers and large enterprise cores requiring ultra-low latency and massive threat inspection throughput.
Delivers unmatched performance and scalability for securing high-bandwidth application
FG XX HA SKUs must be bought in pairs and entitle HA pair to leverage single service contracts (limited to Enterprise, UTP, and ATP bundles only).
Mid – Range Models

FortiGate 100 F
Threat Protection – 1.2 Gbps
USB Port – 1
Console Port – 1
GE RJ45 WAN Ports – 2
GE RJ45 DMZ Port – 1
GE RJ45 FortiLink Ports – 2
GE RJ45 Internal Ports – 12
GE SFP Ports – 2
Description
18x total ports including 14x GE RJ45 (12x Internal, 2x WAN), 2x SFP slots, 1x DMZ port, and 2x FortiLink ports.
128GB SSD onboard storage. Ideal for growing enterprises needing secure SD-WAN and next-generation firewall capabilities.
FG XX HA SKUs must be bought in pairs and entitle HA pair to leverage single service contracts (limited to Enterprise, UTP, and ATP bundles only).

FortiGate 400 F
Threat Protection – 5.5 Gbps
USB Port – 1
Console Port – 1
GE RJ45 WAN Ports – 2
GE RJ45 DMZ Port – 1
GE RJ45 Internal Ports – 16
10GE SFP+ Slots – 4
GE SFP Slots – 4
Description
27x total ports including 16x GE RJ45 Internal, 2x WAN ports, 1x DMZ port, 4x 10GE SFP+ slots, and 4x GE SFP slots.
Equipped with high-performance threat protection and hardware acceleration for large-scale enterprise deployments.
FG XX HA SKUs must be bought in pairs and entitle HA pair to leverage single service contracts (limited to Enterprise, UTP, and ATP bundles only).
Entry Level Models

FortiGate 60 F
Threat Protection – 700 mbps
USB Port -1
Console Port – 1
GE RJ45 WAN Ports – 2
GE RJ45 DMZ Port -1
GE RJ45 Forti Link Ports -2
GE RJ45 Internal Ports – 5
Description
10x GE RJ45 ports (including 7x Internal ports, 2x WAN ports, 1x DMZ port).
10 x GE RJ45 ports (including 2 x WAN Ports, 1 x DMZ Port, 7 x Internal Ports), 128GB SSD onboard storage. FG‑XX‑HA SKUs must be bought in pairs and entitle HA pair to leverage single service contracts (limited to Enterprise, UTP, and ATP bundles only).
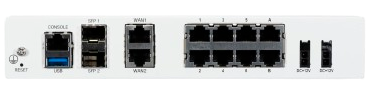
FortiGate 80 F
Threat Protection – 900 Mbps
USB Port – 1
Console Port – 1
GE RJ45 WAN Ports – 2
GE RJ45 DMZ Port – 1
GE RJ45 FortiLink Ports – 2
GE RJ45 Internal Ports – 7
Description
10x GE RJ45 ports (including 7x Internal ports, 2x WAN ports, 1x DMZ port).
10 x GE RJ45 ports (including 2 x WAN Ports, 1 x DMZ Port, 7 x Internal Ports), 128GB SSD onboard storage.
FG XX HA SKUs must be bought in pairs and entitle HA pair to leverage single service contracts (limited to Enterprise, UTP, and ATP bundles only).
Unified SASE
Secure Access, Simplified – Fortinet Unified SASE Solutions
Modern distributed workforces require secure access from anywhere, but securing across branches, remote users, and cloud apps can be complex.
Vays makes it easy for you with Fortinet Unified SASE — SD-WAN, secure web gateway, firewall-as-a-service, and Zero Trust Access in a single cloud-native platform. If you’re feeling fragmented and hard to manage, Vays provides a cohesive approach with potential to scale, regardless of the mediums your team works in.
Zero Trust Network Access (ZTNA)
Zero Trust Network Access (ZTNA) from Vays Infotech delivers identity-based, context-aware access that validates every user and device — whether on or off the corporate network. Application control ensures remote users interact with only the applications they need – and nothing more – providing a secure, scalable alternative to perimeter-based models.
Cloud-based secure web gateway (SWG)
Our combined SWG and FWaaS solutions are designed to intercept web traffic, block harmful content and enforce your policies – wherever your users are. With cloud-profiling and URL filtering, your users enjoy high performance and real-time defense across the protected network.
SD-WAN + security integration
The need to administer SD-WAN and security separately adds complexity and risk. We combine SD-WAN and security in a simple and secure edge-to-cloud architecture that’s easy to manage, with centralized, cloud-based orchestration that automatically directs traffic and enforces application-aware policies—all with integrated threat protection. This combination lowers operational overhead and enhances both performance and security posture.
Complete visibility of users and devices
You can’t protect what you can’t see. With our offering, you get full transparency in terms of user activity, application usage and device behavior – whether users are on the corporate network or working remotely. This continuous monitoring enables rapid threat detection, access auditing, and smarter policy decisions, all from a single dashboard.


Zero Trust Access
Secure Every User, Device & Connection
Concerns about insider threats, vulnerable endpoints, or open doors in remote access? You’re not alone. At Vays, we assist companies deploy Fortinet’s Zero Trust Access out of the gate — where no user, device or request is trusted before verification.
Whether you are protecting third-party sellers or remote staff, we make access based on who, what, where–including device health state at time of access and least-privilege policies where your guardrails. And if access control is your Achilles’ heel, Vays can help you better lock it down.
Identity- and context-based access control
Here at Vays Infotech, we control access through a Zero Trust model, which looks at user identity, device type, location, and behavior when considering access. This Secure Trust Method enables only trusted sources to interact with vital assets—and mitigates compliance risk on your network.
Secure remote and third-party access
Remote work and third-party access have become standard — but they need to be kept in check. Our ZTNA (Zero Trust Network Access) solution provides fine-grained, application-level access to remote employees, vendors, and partners—without opening the door to the overall network.
Real-time device posture checks
Before any connection attempt is permitted, we assess the security state of the device on the fly to see if it complies with security policies (for example, OS version, whether antivirus is updated, and whether encryption settings are enforced). This preemptive validation prevents compromised or noncompliant devices from becoming threat vectors, making access protection that much stronger.
Least privilege policies
Zero Trust model is designed to enforce least privilege access, which means that users only have access to precisely what they need. This lowers your attack surface, helps to mitigate damage from insider threats or compromised accounts, and enables better compliance and governance throughout your IT architecture.
Endpoint Protection Hub
Fortinet Endpoint Protection – Defend Every Device with Vays
But endpoints are the new perimeter — and if you’re only responding to threats after the damage is done, you need to adopt a more intelligent method.
Vays puts you in control, leveraging FortiClient and FortiEDR to provide you with real-time threat protection, AI powered and automated response capabilities as well as unified endpoint security.
From ransomware to zero day attacks, we have your back at every endpoint!
FortiEDR or FortiClient
Enterprises can’t rely on traditional endpoint protection in the ever-evolving threat environment of today. Vays Infotech assists with the implementation of FortiEDR or FortiClient to provide advanced real-time threat detection and responses. These strong endpoint solutions detect and block potentially dangerous behavior, ensuring your systems are safe from new threats before they even strike.
Ransomware, Zero-day threats, and Exploits
Fortinet’s endpoint security detects and blocks zero-day attacks and ransomware threats early in their lifecycle. The solution prevents fileless attacks, memory exploits, and evasive malware while delivering real-time responses to minimize impact and reduce downtime.
Fortinet Security Fabric
Siloed endpoint security management leads to visibility gaps. By connecting FortiEDR and FortiClient directly into the Fortinet Security Fabric, we offer a comprehensive security environment covering endpoints, networks, and clouds. This centralized view and policy enforcement accelerate incident response and simplify security operations.
Automated Response and Remediation
Time is of the essence when it comes to threats. Fortinet’s AI-driven analytics engine delivers real-time alerts and automates remediation to isolate compromised systems, stop malicious processes, and restore functionality without human intervention. This reduces response time from hours to seconds, boosting your defense against advanced attacks.

Cloud Security Hub
From Strategy to Deployment – Get Complete Cloud Security Solutions
Without the proper security posture, moving to the cloud or maintaining multi-cloud workloads can leave your infrastructure vulnerable. That’s where Vays comes in — as leading Fortinet partners in Bangalore we provide you comprehensive security for your AWS, Azure and Google Cloud environments natively from Fortinet.
Architecture to ongoing monitoring, we architect cloud security that grows with your business — with consistent policies, Zero Trust access, and full compliance. If your cloud visibility and/or policy management isn’t feeling so great, Vays can remedy that for you — safely and effectively.
Protect multi-cloud workloads
Security management in multiple clouds is complex and error-prone. At Vays Infotech, we streamline this by enforcing consistent security policies across all your public, private, and hybrid cloud infrastructures. If you are deploying workloads on AWS, Azure or GCP, our solution provides unified control and compliance. This minimizes risk, streamlines operations, and addresses industry standards while maintaining flexibility.
Secure applications and APIs
Built-in WAF (web application firewall) protects your web applications from common threats, preventing possible server breaches and possible geoblocking. With adaptive intelligence and deep packet inspection enabling SSL traffic security, your vital web properties are secured, business continuity is assured, and user productivity is maintained.
Enable Zero Trust access
Old perimeter-based security models don’t work for today’s remote workforce. Our ZTNA approach means that any access request is repeatedly verified with information about identity, device posture, and contextual data. It allows secure and frictionless access to the enterprise applications for remote employees and branch offices, removing over-privileged access and shrinking the attack surface – in both the data center and the public cloud.
Monitor real-time threats
Visibility is the name of the game when it comes to protecting against cyber security threats. With our centralized cloud-native monitor and analytic engine, you get instant visibility into security occurrences in the cloud workloads, endpoints and networks. The combined dashboard allows you to proactively detect threats, respond to incidents quickly and report compliance easily — all in a single pane of glass. Keep one step ahead of attackers and respond to threats with data-driven decisions.

Operational Technology (OT) Security
From Factory Floor to Field Sites – Secure Your OT Infrastructure
Industrial networks frequently have outdated security — and regular IT firewalls aren’t sufficient. If you are wrestling with legacy systems, sensitive uptime demands, regulations and audit. Vays can help.
Protect your SCADA, PLCs, and ICS environments using Fortinet’s ruggedized appliances and deep protocol inspection mitigating the threat and providing secure control in one solution with no impact to operations. Whether separating IT and OT or reaching IEC 62443 compliance, we address your OT security problems—head to tail.
Ruggedized FortiGate for Legacy & Smart Systems
Many traditional industrial systems have no built-in security, while modern smart devices add their own weak points. Vays Infotech covers both ends of the range with ruggedized FortiGate firewalls rated for harsh conditions. They deliver threat protection, segmentation, and secure remote access for OT environments, substations, and manufacturing plants.
Real-Time OT Threat Monitoring
Our security offerings provide continuous monitoring down to the field devices, PLCs, and HMIs. This ensures that threats can be detected promptly and a proactive defence pursued with as little disruption of essential functions as possible.
Deep Protocol Inspection for OT Traffic
Industrial networks run on specialized protocols like Modbus, DNP3 and BACnet —which traditional IT security tools still tend to overlook. Our deep protocol inspection enables us to analyse OT traffic “as it flies” and to alert on anomalous behavior, policy violations, and potential threats without interfering with production. This reduces the IT-OT gap to the minimum and guarantees accurate threat detection in ICS/SCADA environments.
Regulatory Compliance Made Simple
Compliance isn’t a matter of checking a box — it’s a matter of survival for operators of critical infrastructure. Our OT security solutions are architected to assist you in comply with international benchmarks like IEC 62443, NIST CSF, and ISO 27001. With integrated testing, auditing tools, access controls, and reporting we walk with you along the path to a secure, compliant and resilient environment.
Benefits of Partnering with Vays Infotech
Comprehensive support
At Vays Infotech, we provide comprehensive Fortinet cybersecurity solutions including firewalls, endpoint and SD-WAN, SASE, Zero Trust Access. Full protection across your network, cloud and edge. We are not just offering the solutions—we offer continued support and proactive threat management.
Customer Centric Approach
Our team is dedicated to your success and is certified. From pre-sales consultation to post-deployment support, we collaborate with your IT department to learn your specific requirements, and ensure an optimized installation of Fortinet equipment. We put customers first, so you’ll always have up-to-date security.
Industry Expertise
With decades of industry expertise and a strong focus on Fortinet, Vays Infotech provides extensive technical knowledge and real-world experience. If you are a small business, or a large enterprise, we make it easy for you to take advantage of Fortinet’s Security Fabric.
Seamless integration and scalability
Being a certified fortinet partners in Bangalore, we make sure that your IT frameworks are better integrated with the fortinet solutions while ensuring nothing goes out of place. All of our deployments have scalability in its DNA—this means as you grow, so too, does your security.
