Access Control and Surveillance as IP Infrastructure
Access Control and Surveillance as IP Infrastructure
Devices and Applications in the corporate environment have become increasingly IP-based. The IP which used to be always there on the backend, at the integration level, is finding a place in front end user application as well. The simplicity and familiarity to configure are the two main reasons which drive the IP adoption.
The recent two new applications, which were traditionally non-IP or non-IT, are access control and surveillance, to be added to IP Infrastructure. Both these applications are beside whatever have already transformed like voice communication (SIP Now), Storages, Wireless access etc. Access control and Surveillance, both these devices used IPs; only in the head-end side where the storage media or controllers are connected to the network infrastructure. Today CCTV cameras and the access controller up to the sensor level, are IP enabled and ready for deployment as part of the IT infrastructure.
These changes have been gradually happening for the last 10 years. Because of the ubiquitous nature of IP in the infrastructure, it is logical for any manufacturer to adopt IP for their applications to be part of the infrastructure. All the Low voltage applications, including the Industrial Automation, will morph or change to IP Infrastructure

What One Should Know About Firewall Renewal?
Firewall A Firewall is a system /a network security device which can be an appliance (Custom Hardware/ Software Combo) or a Software Application residing on a Commercial Server Hardware. Irrespective of the type, they are critical in a Network as it is in the path of...
Case Study On EndPoint Security And DLP For NBFC (Microfinance Company), India
The client, is a Microfinance institution committed to working towards women’s economic empowerment. It is providing innovative and affordable financial products to women from unbanked sections in society in both rural and semi urban areas. It has branches in 16...
Enterprise Service Desk
According to the Information Technology Infrastructure Library (ITIL), an enterprise service desk comes as the primary IT function within the IT Service management. The main motive or intent for creating such an IT function is to create a Single Point of Contact...
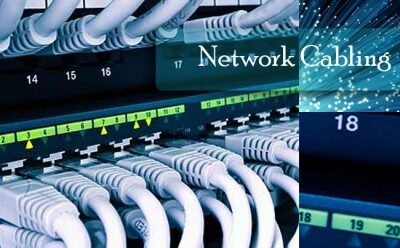
Network Diagnostic Using TDR Commands
A Time Domain Reflectometry (TDR) is an electrical instrument that uses time-domain reflectometry to characterize and locate faults in metallic cable (for example, twisted pair wire or coaxial cable). It can also be used to locate discontinuities in a...
Managed Firewall Services
A firewall or UTM’s key objective is to stop rogue or unauthorized access by hackers and costly business disturbances. The firewall, UTM or such devices for any Specialized Managed Firewall Services must be provided, distributed, updated and patched as a process and...
IT Infrastructure Service-The key component of success in business today
IT Infrastructure plays a vital role in the success of any business in the present competitive world. IT infrastructure service and solution is the key component of the success in business today. There are many reasons for this but one of the main acceptable reasons...
Access Control and Surveillance as IP Infrastructure
Devices and Applications in the corporate environment have become increasingly IP-based. The IP which used to be always there on the backend, at the integration level, is finding a place in front end user application as well. The simplicity and familiarity to...
Point To Point Outdoor Wireless
Know More About Point To Point Services And Point To Multipoint Products A Wireless Point-to-Point, connection is a telecommunications connection between two premises or endpoints. A telephone call is a sample example of a Point-to-Point...
Technology Consulting Services
When making a huge amount of software investment, Company needs an experienced consultant to provide technology insight and able to examine the upcoming path and the trend; this is where Vays Infotech consultants come into the picture. Our experienced technology...
Network Security
Introduction To Network Security Security is a fundamental component of every IT Infrastructure design. When planning, building, and operating a network facility, one should understand the importance of Information Security and incorporate Robust Security Policy....